Network Topologies for Resilient Engineering Teams
A topology of how I speak, listen, and belong
I’m a systems engineer who believes architecture is culture. As I share on my about page, I spend my days designing startup-grade, secure applications and my nights examining the human protocols that make teams work. Recently I realised that the same diagrams I draw for routers and firewalls also describe how we talk, lead, and belong. Below is the map I now keep on my whiteboard—and in my relationships.
If you enjoy abstractions that turn into deployable software, check out my Data Breach Scanner or browse the rest of my projects.
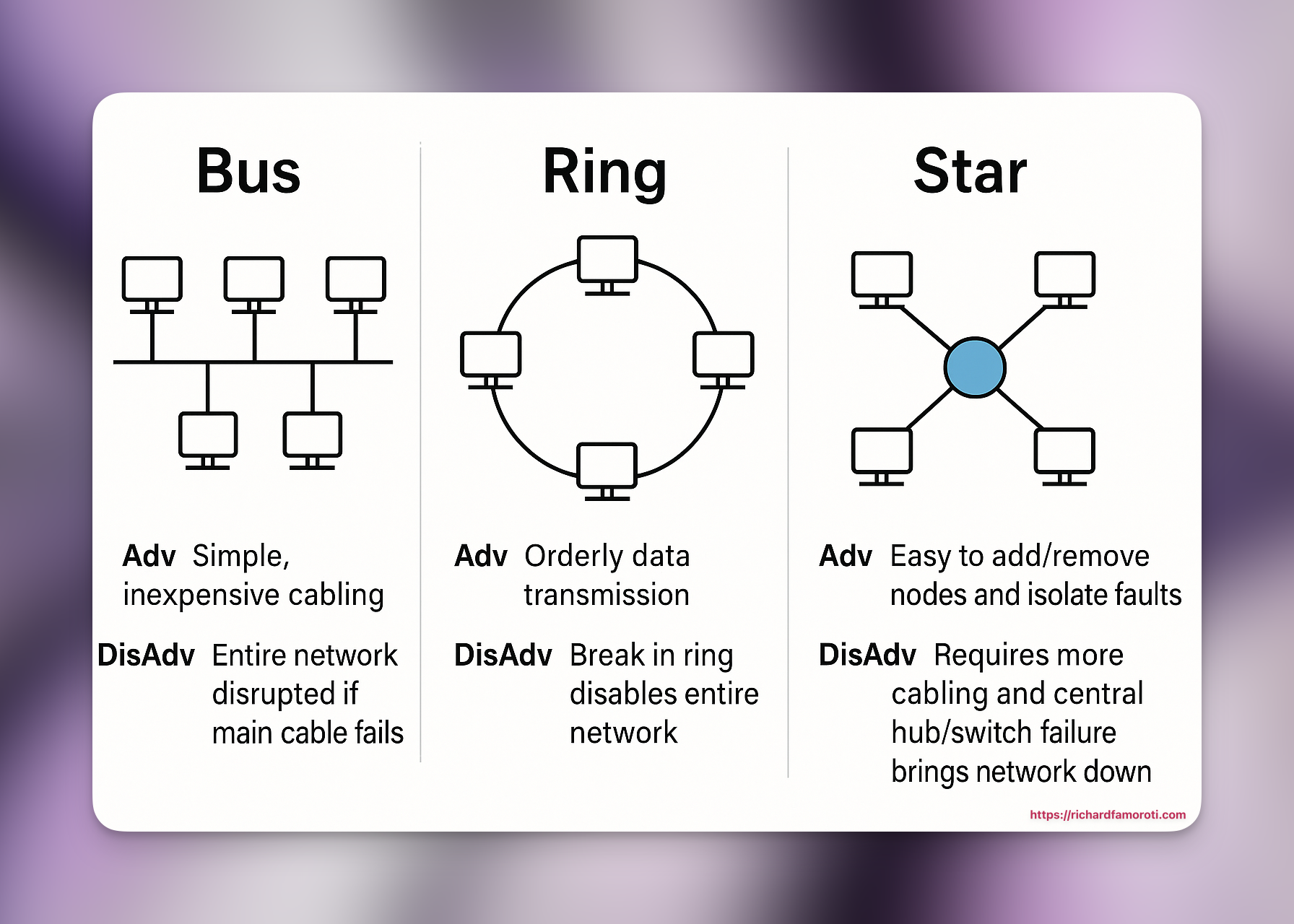
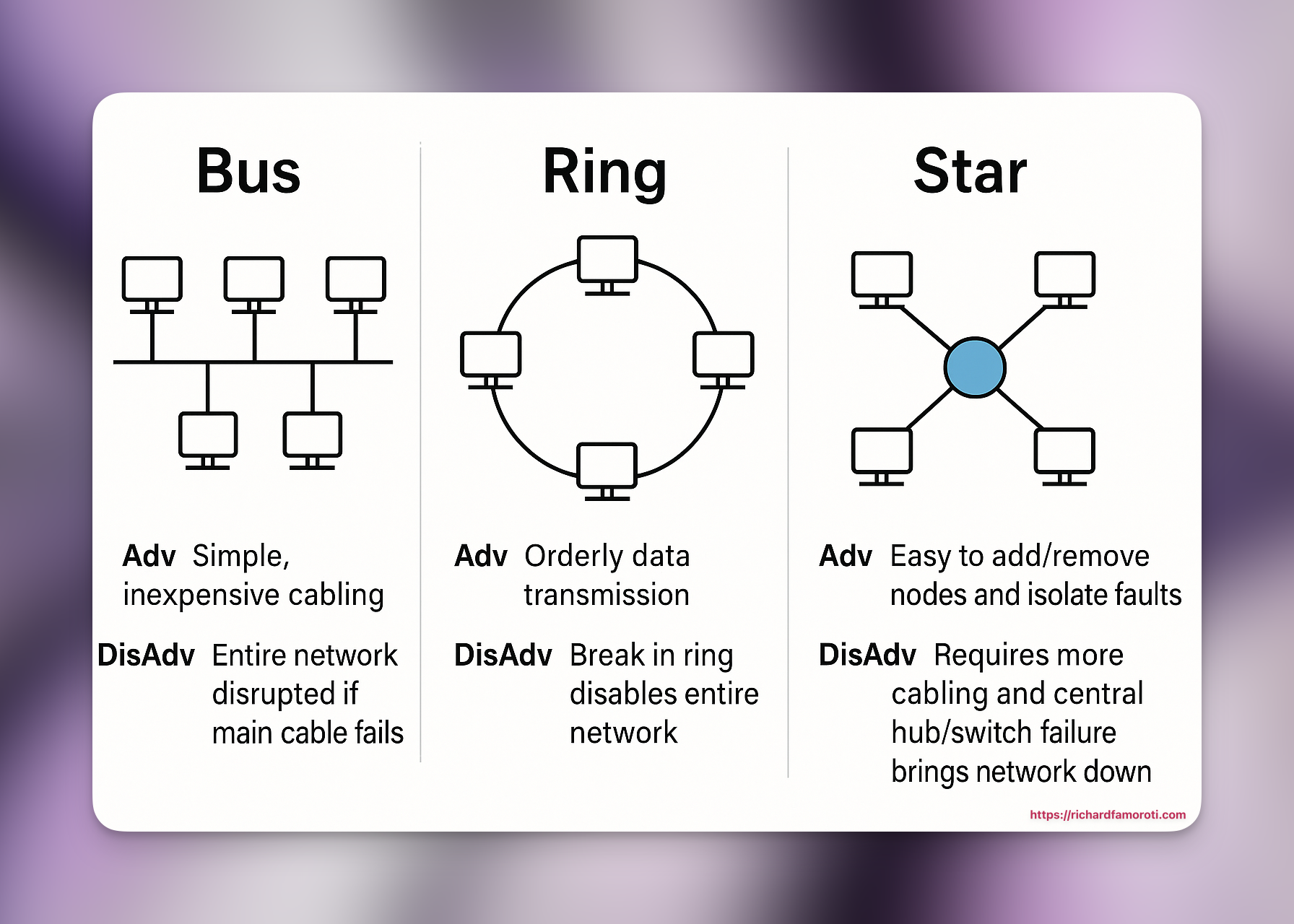
1. Point-to-Point — “You and I”
Two nodes. One line. No intermediaries. When I write “you and I,” I’m invoking the simplest and most intimate network design: point-to-point (1:1). The signal is direct. There’s no ambiguity about who needs to hear what, and the latency—emotional and technical—is minimal.
Advantage (in engineering and life): Clarity. Whether it’s an RPC call or a difficult conversation, I get fast feedback with minimal noise.
Disadvantage: It doesn’t scale. Maintaining every relationship—or microservice—this way burns out both the engineer and the network.
2. Star — “You guys”
A hub at the center, spokes stretching outward. When I say “you guys,” I become (or appoint) a central switch. I broadcast updates to many, but all roads route through me. This is infrastructure-level leadership: I curate, coordinate, and—when necessary—throttle.
Advantage: Efficiency. I can push releases or inspiration to multiple nodes at once while keeping the topology organized.
Disadvantage: I become a single point of failure. If the hub is overloaded or offline, the entire conversation collapses.
3. Ring — “We, us, the tribe”
Each person is a link in a chain. Messages pass from one to the next in a loop. When I use “all of us,” I’m naming a ring topology: a community where responsibility is distributed. No one hogs bandwidth; cooperation is coded in.
Advantage: Order and equality. Everyone holds the token eventually—much like a well-designed consensus algorithm.
Disadvantage: A single break silences the circle. Hurt one link, and the loop is broken. Without redundancy, we all go dark.
4. Bus — “Our individualism, connected by bloodline”
Picture a single backbone cable with T-connectors branching out. That’s the bus—our family, our lineage. Each of us is tapped into a shared trunk called history.
Advantage: On-boarding is instant. You’re born, you’re plugged in, and the backbone carries the story.
Disadvantage: One fault on the spine—trauma, secrecy, unpatched firmware—and everyone’s packets suffer.
Collision Domains, Bandwidth, and Noise
In a bus, two people can “speak” at once and their signals collide. That’s a family dinner during peak season. In a star, the hub moderates collisions; in a ring, the token does. In my teams, I create collision-avoidance protocols—stand-ups, RFC templates, and escalation policies.
Bandwidth isn’t just Mbps; it’s emotional capacity. I’ve overloaded links before, sending too much truth without compression. I’ve also underutilized channels, going quiet when I should have transmitted.
Noise is everywhere: gossip, assumption, the ghosts of past messages still echoing in the line. So I encrypt—not to hide, but to keep meaning intact. Integrity checks matter. “Did you get me?” is my human checksum.
Redundancy, Failover, and Mesh Dreams
Networks survive by redundancy. I try not to rely on one hub, one ring, one bus. Over time, I’ve been building a mesh—multiple pathways, friendships that bypass legacy backbones, communities that reroute when a node fails. You can see this philosophy in action across my portfolio of projects.
Failover is resilience: when one path drops, another stands up. I’m not done building that yet—but I’m already laying fiber between the versions of myself I trust.
Protocols: The Rules of Engagement
Every topology needs a protocol. TCP/IP has SYN and ACK. We have hello and how are you, we have contracts, we have boundaries.
- Handshake: A ritual to synchronize expectations. In code, that’s negotiation of API versions; in life, it’s clarifying roles.
- Flow Control: Knowing when to slow down, when to buffer emotion until the receiver can process.
- Timeouts: Not every silence is rejection—sometimes a packet is just delayed.
I value idempotent messages—things safe to repeat: “I appreciate your work.” “I was wrong.” “Let’s try again.”
Security: Who Gets Root?
In secure systems, you can’t casually hand out root. In my life, I can’t give root access to anyone, including the loudest voice inside my head. So I run sudo prompts: Are you sure? Type your password to make this change to who you are.
Secrets operate on the principle of least privilege. I open-source my lessons, not my vulnerabilities. The former scales; the latter needs point-to-point trust.
Maintenance Windows and Upgrades
Sometimes I take the network down for maintenance. That’s what retreats and sabbaticals are: Patch Tuesday for the soul. Apply updates, reboot, come back with stronger encryption and clearer logs.
Announcing downtime prevents false alarms: I’m not ignoring you; I’m upgrading the router.
The Final Ping
These topologies aren’t just diagrams—they’re the architecture of my relationships. And like any good engineer, I keep testing:
- Ping the old friend (1:1). Latency acceptable? Packet loss?
- Broadcast a new idea (Star). Did the hub hold? Did the spokes respond?
- Sit in a circle (Ring). Did everyone get the token?
- Trace the backbone (Bus). Where’s the hum of ancestry leaking into the present?
I’m learning that the topology can change mid-sentence. I can switch from “you guys” to “you” when I need to get through, widen the ring when someone new joins, splice the bus when the backbone corrodes.
In the end, I want resilient networks—of code, of people, of self. Failure will come, but when it does, we’ll already have another path.
Let’s Build Together
I specialize in building secure, scalable software solutions. If you’re looking for expertise in network-centric system design or resilient team communication, explore my other projects or get in touch to discuss your needs.